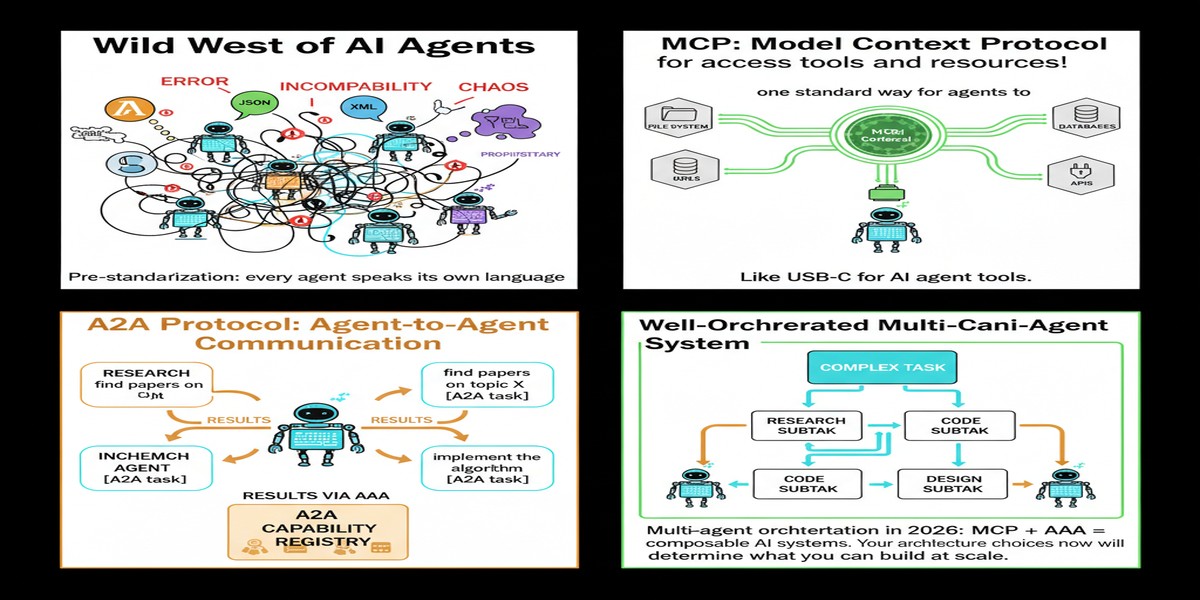
We're at an inflection point in multi-agent systems that most practitioners haven't fully recognized yet. For the past three years, every team building multi-agent AI has been inventing their own protocols, their own state management, their own coordination patterns. This worked fine when multi-agent systems were research experiments. It's becoming a serious liability now that they're production infrastructure.
The January 2026 paper The Orchestration of Multi-Agent Systems is one of the clearest treatments I've seen of the emerging standardization landscape — specifically around MCP (Model Context Protocol) and the Agent2Agent (A2A) protocol. If you're building multi-agent systems for enterprise use, this is the paper that will help you understand what your architecture is going to look like in two years, whether you plan for it or not.
Paper: The Orchestration of Multi-Agent Systems: Architectures, Protocols, and Enterprise Adoption Authors: Apoorva Adimulam, Rajesh Gupta, Sumit Kumar Published: arXiv:2601.13671, January 2026
The State of Multi-Agent Coordination Before Standards
Before getting into the paper's contributions, it's worth naming the problem clearly.
Current multi-agent systems communicate through ad hoc mechanisms: custom message formats, proprietary APIs, bespoke state management. When you use CrewAI, LangGraph, AutoGen, or a homegrown framework, each has its own way of:
- Passing context between agents
- Expressing task delegation
- Sharing tool access
- Managing conversation history
- Signaling errors and requesting human intervention
This fragmentation creates several problems:
Integration overhead. Every integration between two systems built on different frameworks requires custom translation layers.
Tool duplication. The same tool (a web search capability, a database connection, a code execution environment) gets implemented differently in each framework.
Audit impossibility. Understanding what happened across a multi-agent workflow spanning different frameworks requires stitching together incompatible logs.
Vendor lock-in. Once you've built a complex workflow in one framework's model, migration is expensive.
The paper frames MCP and A2A as the infrastructure for solving these problems — essentially, defining the "HTTP of multi-agent coordination."
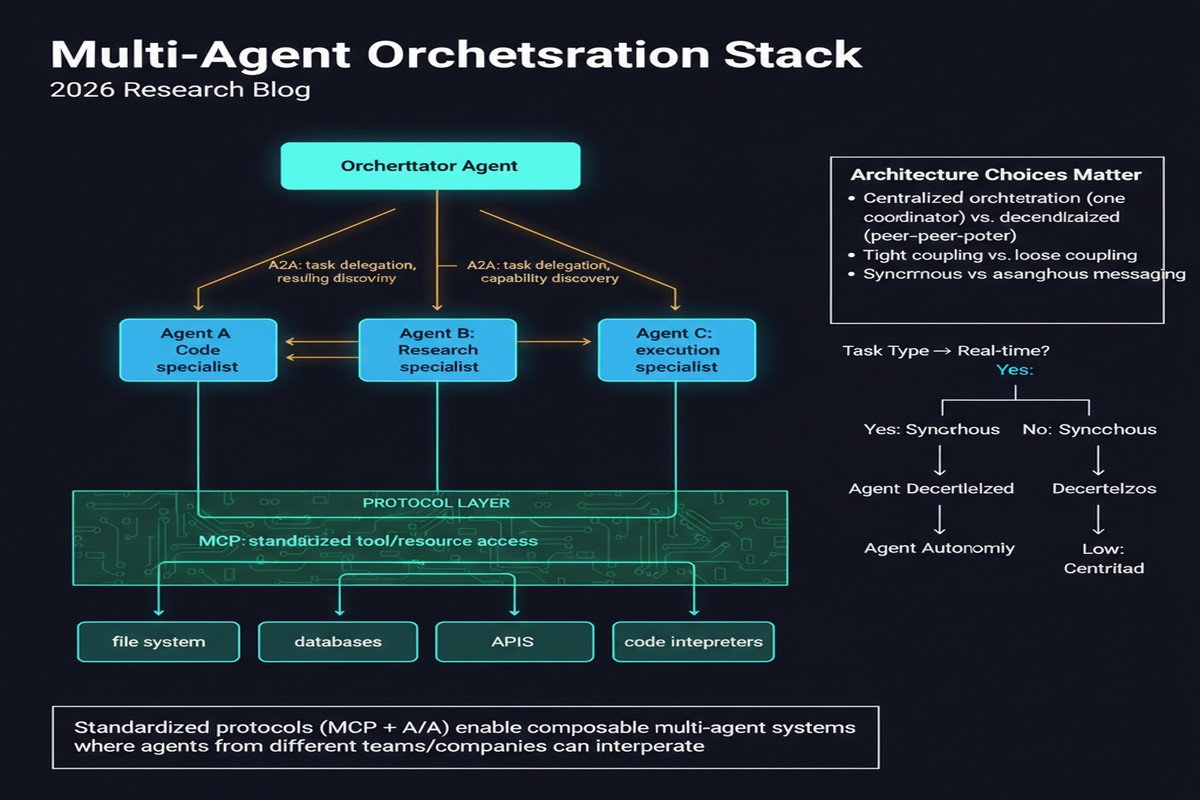
The Two Protocols
Model Context Protocol (MCP)
MCP standardizes how agents interact with tools and external resources. Before MCP, each agent framework had its own way of defining tools, calling them, and parsing results. MCP creates a common interface that any tool provider can implement and any agent can call.
The key abstraction is the MCP server — a standardized process that exposes tools (callable functions), resources (data that agents can access), and prompts (templated instructions) via a consistent protocol. An agent with an MCP client can use any MCP server's capabilities without knowing how they're implemented.
graph LR
subgraph Before MCP
A1[Agent Framework A] -- custom API --> T1[Tool 1]
A1 -- different API --> T2[Tool 2]
A2[Agent Framework B] -- yet another API --> T1
A2 -- incompatible interface --> T2
end
subgraph With MCP
B1[Any MCP Agent] -- MCP protocol --> S1[MCP Server 1\nexposes Tools A, B]
B1 -- MCP protocol --> S2[MCP Server 2\nexposes Tools C, D]
B2[Any other MCP Agent] -- MCP protocol --> S1
B2 -- MCP protocol --> S2
end
The paper's coverage of MCP is thorough on the protocol mechanics but relatively light on enterprise adoption challenges. I'll add some color here from practical experience: the biggest friction in MCP adoption isn't the protocol itself, it's the operational model for MCP servers. Who owns them? Who maintains them? Who's responsible when they fail? These governance questions aren't answered by the protocol.
Agent2Agent (A2A) Protocol
Where MCP handles agent-tool interactions, A2A handles agent-to-agent interactions — delegation, negotiation, result passing, and collaboration between agents.
A2A defines:
- How one agent expresses a request to another (task specification, context, constraints)
- How agents negotiate capabilities and accept or decline tasks
- How results are communicated back (structured output formats, error conditions)
- How agents signal status during long-running operations
This is the protocol that makes "orchestrator-worker" architectures interoperable. An orchestrator using one framework can delegate to a specialist agent built on a different framework, via A2A, without either side needing to know the other's internals.
sequenceDiagram
participant O as Orchestrator Agent
participant S1 as Specialist Agent 1\n(different framework)
participant S2 as Specialist Agent 2\n(different framework)
O->>S1: A2A: Delegate subtask A\n(context, constraints, expected output format)
S1-->>O: A2A: Acknowledge, status: in_progress
O->>S2: A2A: Delegate subtask B\n(parallel execution)
S2-->>O: A2A: Acknowledge, status: in_progress
S1-->>O: A2A: Complete, result: {...}
S2-->>O: A2A: Complete, result: {...}
O->>O: Synthesize results, continue workflow
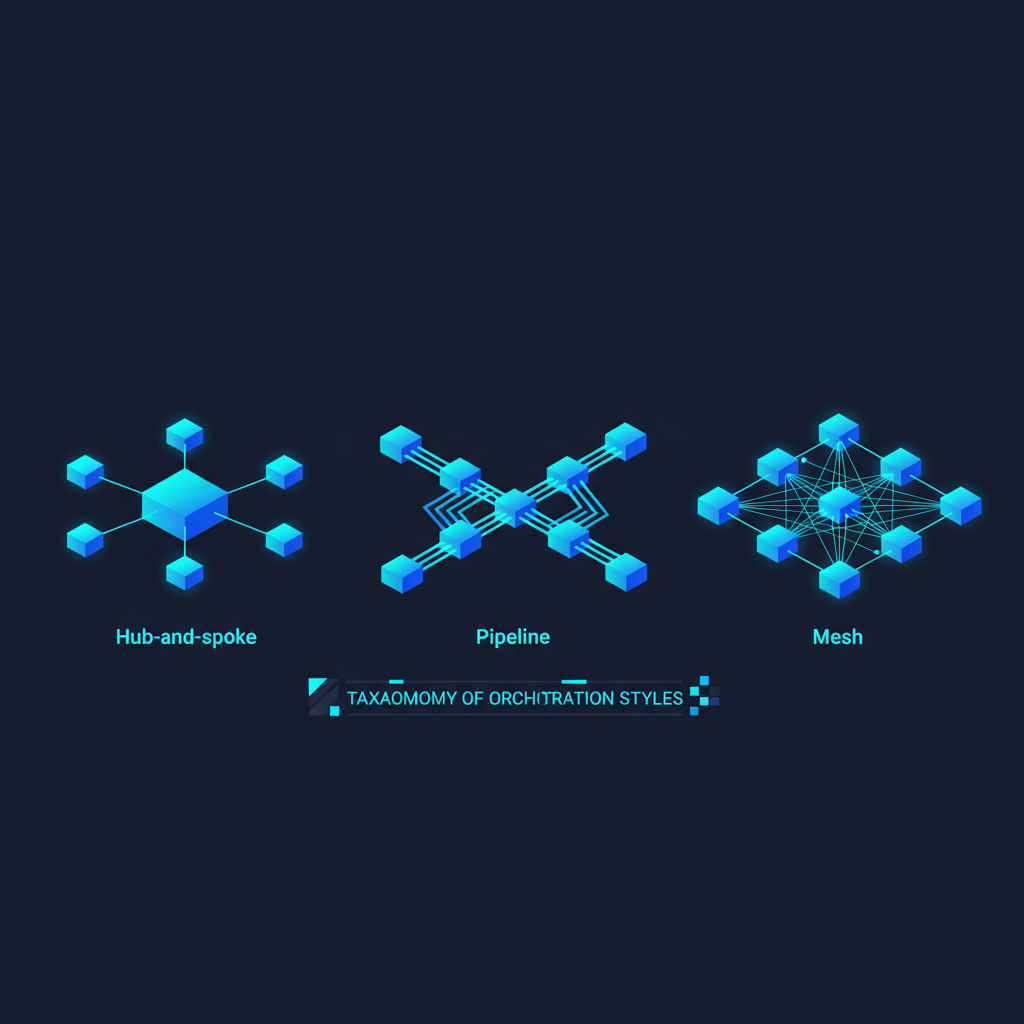
The Four Pillars of Enterprise Orchestration
Beyond the protocols, the paper organizes enterprise multi-agent orchestration around four operational concerns:
Planning: How does the orchestrator decompose goals into agent tasks? The paper covers several patterns — hierarchical planning, market-based allocation, consensus-driven planning — and their enterprise trade-offs.
Policy enforcement: How do you ensure agents operate within organizational constraints? This is the intersection with governance (AGENTSAFE territory) but focused on real-time enforcement rather than after-the-fact audit.
State management: How do you maintain coherent world state across a distributed set of agents? The paper covers eventual consistency approaches and their limitations for state-sensitive workflows.
Quality operations: How do you detect quality degradation in agent outputs, trigger reprocessing, and maintain SLAs? This is the operational monitoring dimension that most academic multi-agent papers ignore.
Why This Matters
The standardization argument is the paper's most important contribution, and it's more urgent than most practitioners appreciate.
Right now, the multi-agent ecosystem is in the "Cambrian explosion" phase — massive diversity, rapid innovation, no standards. This phase is productive for research and early exploration. It's problematic for enterprise adoption, which requires:
- Predictable integration costs. If every new agent system requires a custom integration, the total cost scales quadratically with the number of systems.
- Reliable interoperability. Enterprise workflows don't respect framework boundaries. A workflow that spans a customer service agent, a backend data agent, and a content generation agent needs them to communicate reliably.
- Auditable operations. Regulated industries need to trace exactly what happened in an agent workflow. This requires consistent logging formats.
MCP and A2A provide the standardization that enterprise adoption requires. The teams that learn these protocols now and build their architectures around them will have a significant advantage over teams that learn them when they become mandatory.
My Take
I'm genuinely bullish on the MCP and A2A protocols, but I have reservations about the pace of adoption framing in this paper.
The paper presents MCP and A2A as already on a clear path to standardization. I think that's correct directionally but premature as a statement of current state. Protocol standardization requires ecosystem-wide coordination that's still in progress. There are competing approaches, and the final form of these protocols may look quite different from their current versions.
What I'd push back on specifically: the paper is too optimistic about A2A adoption in enterprises. MCP adoption is real and accelerating — the tool abstraction layer is an obvious win. A2A is more ambitious because it requires agents to expose capabilities and accept delegation in a standardized way, which creates security surface area that enterprise security teams will scrutinize heavily.
The security implications of A2A deserve more attention than the paper gives them. When any A2A-compliant agent can delegate to any other, you've created a large potential attack surface. An attacker who compromises one agent could use A2A to pivot to agents with broader access. The paper mentions this but doesn't give it the depth it deserves.
Still: this is the most practically useful architectural overview of enterprise multi-agent systems that I've seen in the academic literature. The MCP/A2A framing is the right frame for thinking about where this space is going. If you're building multi-agent infrastructure, read this paper before finalizing your architecture.
Further Reading
- arXiv: 2601.13671
- Related: Towards a Science of Scaling Agent Systems (2512.08296) for empirical architecture guidance
- Related: Multi-Agent Collaboration Mechanisms survey (2501.06322) for broader taxonomy
- Primary: MCP specification at modelcontextprotocol.io